Facing tomorrow’s quantum hackers today
When it comes to computing ability, the general rule of thumb is more is better. Quantum computers promise to feed this hunger. Their immense processing power derives from their ability to store and handle significantly larger volumes of data than classical bit-driven computers. As a result, a future quantum computer, in theory, could take minutes to solve problems that take classical computers tens of thousands of years.
The possibilities of such computing power are enormous. Sifting through libraries of molecular combinations to accelerate drug discoveries, tightening logistics planning, boosting computational chemistry, fine-tuning weather forecasting accuracy, and strengthening financial modeling are just a few of the many applications waiting in the wings.
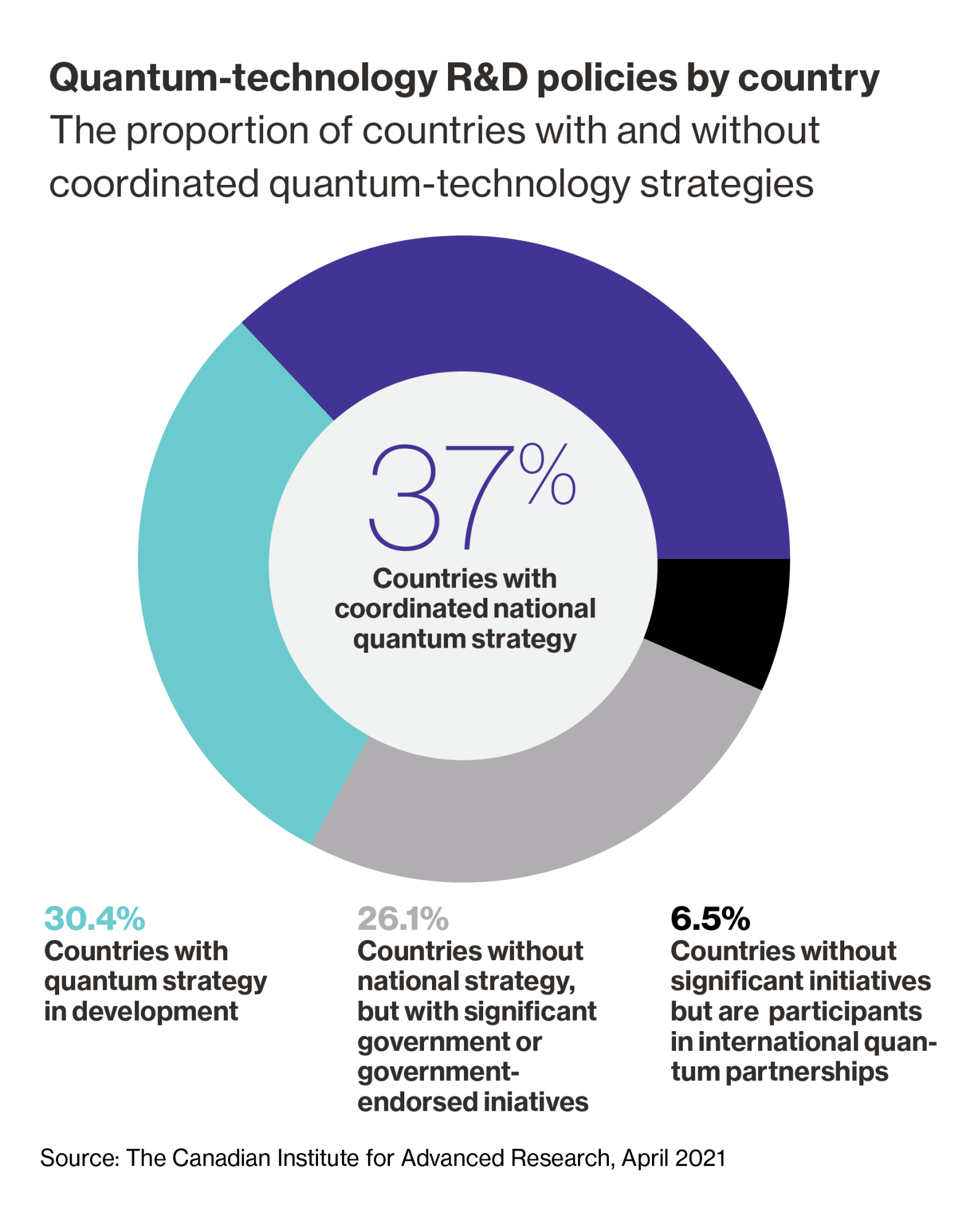
Governments and private companies around the world recognize the potential of quantum computing—which could create “value of $450 billion to $850 billion in the next 15 to 30 years,” according to estimates from a 2021 report from Boston Consulting Group—and are working to develop their own quantum strategies and research initiatives.
Bracing for the power of quantum
However, as quantum technology continues to advance, one dark cloud lurks on the horizon. Hackers can one day use this processing power to break public-key cryptography systems, which form the basis for today’s secure interactions over the Internet, as well as other systems such as public-key infrastructure, code-signing systems, secure email, and key-management systems. Experts warn this is a major threat to modern digital security that needs to be tackled now. “It will completely break these crypto systems,” says Dustin Moody, a mathematician at US-based National Institute of Standards and Technology (NIST).
Although a full-scale quantum computer has yet to become reality, the danger is imminent. Duncan Jones, head of cybersecurity at a Cambridge- and Colorado-based quantum computing company, Quantinuum, says he’s concerned about a particular problem. “If I send you some encrypted data today and somebody records that, they can break into that later on,” says Duncan. “They don’t need a quantum computer today to break into it. They can just patiently sit on that data and they can then decrypt in the future.”
To defend against such quantum attacks, post-quantum cryptography is emerging as an efficient and effective solution. It refers to a set of new cryptographic algorithms, in particular public-key algorithms, that can be implemented using today’s classical computers.
There is growing urgency for enterprises of all sizes and across all industries, as well as public institutions and other organizations, to make their systems crypto-agile and adopt such quantum-resistant algorithms in their security frameworks. Companies and organizations cannot afford to wait and see how the quantum-computing landscape evolves. “The cost will blow up if it is adopted after quantum computers are established,” says Jung Hee Cheon, professor of mathematics at Seoul National University in South Korea. Given the high stakes, a proactive, rather than reactive, stance toward such threats becomes crucial.
Download the full report.
This content was produced by Insights, the custom content arm of MIT Technology Review. It was not written by MIT Technology Review’s editorial staff.